Blog Posts & Articles
Cybersecurity Updates, Recent Vulnerabilities, and Hacking Guides.
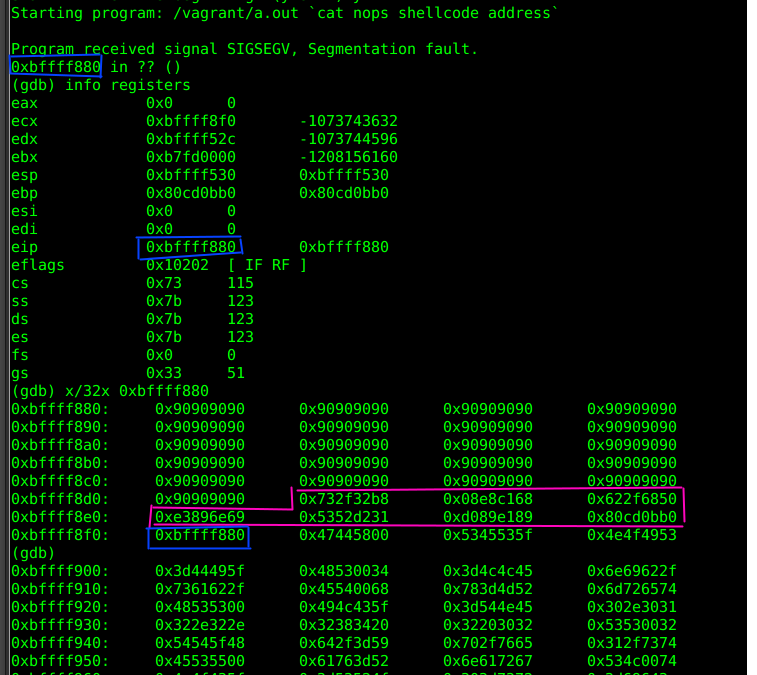
Buffer Overflow Vulnerabilities: Understanding and Mitigating the Risk Introduction In the realm of cybersecurity, buffer overflow vulnerabilities have long been a prevalent issue. These weaknesses can lead to severe consequences, including unauthorized access to...

Cybersecurity Certifications Are Not Enough for Your First Job — Here’s Why
You have the certifications. So why aren’t you getting hired? Discover why cybersecurity certifications alone are not enough to land your first job, and learn what employers actually look for — with 3 real-world scenarios.
No Results Found
The page you requested could not be found. Try refining your search, or use the navigation above to locate the post.
Stay Secure with the Latest Cyber Security News and Trends
Threat Landscape
IoT Security
Social Engineering
Zero Trust
Incident Response
Cloud Safety
Know the Latest on Cyber Security
How Most Data Breaches Are Caused by Insider Threats (With 3 Real Cases)
The biggest cybersecurity threat isn’t hackers from the outside — it’s the people already inside your organization. Learn how insider threats cause most data breaches, explore 3 real-world cases including the NSA, Capital One, and Tesla, and discover how to defend your organization.
Cybersecurity Certifications Are Not Enough for Your First Job — Here’s Why
You have the certifications. So why aren’t you getting hired? Discover why cybersecurity certifications alone are not enough to land your first job, and learn what employers actually look for — with 3 real-world scenarios.
Understanding QoS Modes: A Clear Guide for New Network Administrators
Port-Based QoS vs 802.1p/DSCP QoS: What’s the Difference? If you’re new to networking, you’ve probably seen QoS settings like Port-based QoS and 802.1p/DSCP-based QoS on your router or switch. But what do these terms actually mean? And which one should you use? This...
Insecure LDAP vs Secure LDAP: Risks, Benefits, and Best Practices
LDAP plays a critical role in enterprise identity management, but when deployed insecurely, it becomes a major cybersecurity liability. With over 30 years of cybersecurity experience, this guide explains the difference between Insecure LDAP and Secure LDAP (LDAPS),...
All Categories
Red Teaming
Blue Teaming
Pentesting
Endpoint Security
Network Defense
Identity and Access Management
Cryptography
Compliance and Regulations
Secure Coding
Physical Security
Threat Intelligence
Malware Analysis
Stay Up to Date With The Latest News & Updates
Access Premium Content
Unlock a treasure trove of expert cybersecurity insights, in-depth analyses, and exclusive reports. Go premium and stay ahead of the digital threats with our top-tier content
Join Our Newsletter
Stay informed and vigilant. Subscribe to our newsletter for the latest in cybersecurity trends, threats, and best practices—delivered straight to your inbox
Follow Us
Dive deeper into the world of cybersecurity. Follow us on our social channels for daily insights, tips, and exclusive content




