Blog Posts & Articles
Cybersecurity Updates, Recent Vulnerabilities, and Hacking Guides.
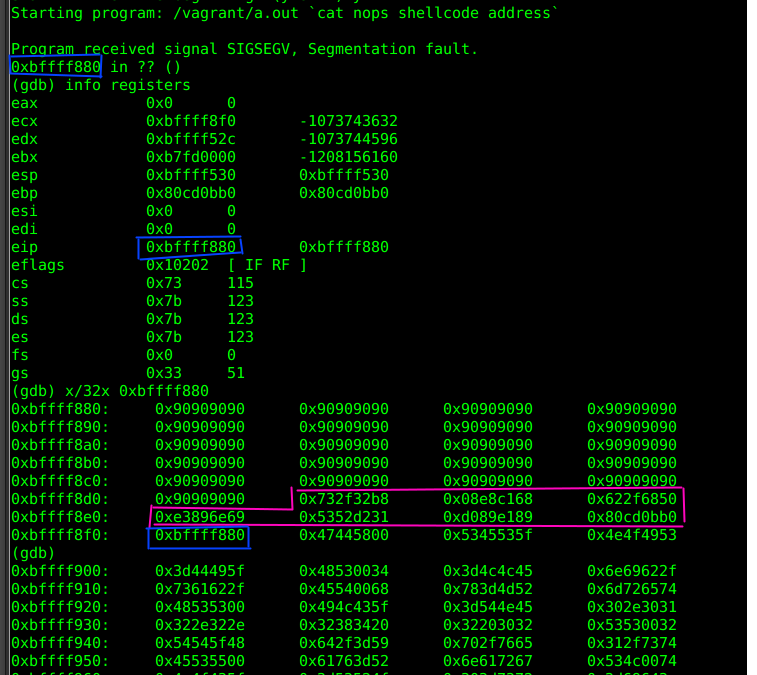
Buffer Overflow Vulnerabilities: Understanding and Mitigating the Risk Introduction In the realm of cybersecurity, buffer overflow vulnerabilities have long been a prevalent issue. These weaknesses can lead to severe consequences, including unauthorized access to...

Third-Party Risk in 2026: How a Forgotten Vendor Became the Most Expensive Breach Vector
A senior third-party risk practitioner walks through three vendor-mediated breaches and the four-pillar architectural playbook that contains the blast radius.
No Results Found
The page you requested could not be found. Try refining your search, or use the navigation above to locate the post.
Stay Secure with the Latest Cyber Security News and Trends
Threat Landscape
IoT Security
Social Engineering
Zero Trust
Incident Response
Cloud Safety
Know the Latest on Cyber Security
Cyber Talent in 2026: A Senior Practitioner’s Sunday Letter on the CEO Question Most Boards Refuse to Ask
A senior practitioner’s Sunday letter to every CEO and board on the cyber talent question — the workforce decisions that quietly govern every other security outcome.
Third-Party Risk in 2026: How a Forgotten Vendor Became the Most Expensive Breach Vector
A senior third-party risk practitioner walks through three vendor-mediated breaches and the four-pillar architectural playbook that contains the blast radius.
Credential Stuffing in 2026: The Industrialized Attack That Looks Like Normal Traffic
A senior identity protection practitioner walks through three credential stuffing engagements and the four-pillar defense that actually holds up in 2026.
Detection Engineering Maturity in 2026: Why Most SOCs Have More Rules Than Insights
A senior detection engineer walks through three SOC engagements where rule count masked declining incident output, and the four-practice playbook that fixes it.
All Categories
Red Teaming
Blue Teaming
Pentesting
Endpoint Security
Network Defense
Identity and Access Management
Cryptography
Compliance and Regulations
Secure Coding
Physical Security
Threat Intelligence
Malware Analysis
Stay Up to Date With The Latest News & Updates
Access Premium Content
Unlock a treasure trove of expert cybersecurity insights, in-depth analyses, and exclusive reports. Go premium and stay ahead of the digital threats with our top-tier content
Join Our Newsletter
Stay informed and vigilant. Subscribe to our newsletter for the latest in cybersecurity trends, threats, and best practices—delivered straight to your inbox
Follow Us
Dive deeper into the world of cybersecurity. Follow us on our social channels for daily insights, tips, and exclusive content