What Is LDAP?
Lightweight Directory Access Protocol (LDAP) is used to authenticate users and manage directory services such as Active Directory, user credentials, groups, and access permissions across networks.
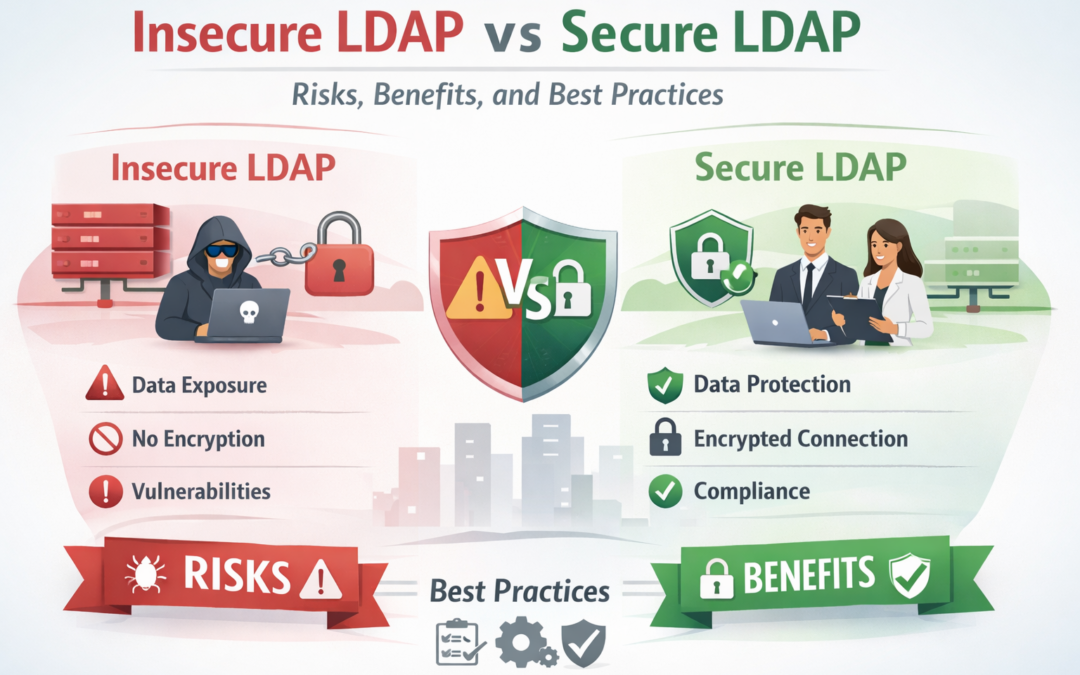
What Is Insecure LDAP?
Insecure LDAP refers to LDAP communication transmitted in clear text over port 389. Credentials, queries, and responses are sent without encryption, making them vulnerable to interception.
Key Risks of Insecure LDAP
- Plaintext transmission of usernames and passwords
- High exposure to man-in-the-middle (MITM) attacks
- Credential harvesting through network sniffing
- Violation of security and compliance standards (PCI-DSS, HIPAA, SOC 2)
What Is Secure LDAP (LDAPS)?
Secure LDAP (LDAPS) encrypts LDAP traffic using TLS/SSL, typically over port 636. This ensures authentication data and directory queries remain confidential and tamper-proof.
How Secure LDAP Works
- Encrypts authentication traffic using TLS certificates
- Prevents credential interception
- Ensures data integrity between clients and directory servers
Insecure LDAP vs Secure LDAP: Key Differences
- Encryption: Insecure LDAP = none | Secure LDAP = TLS-encrypted
- Credential Safety: Insecure LDAP exposes credentials | Secure LDAP protects them
- Compliance: Insecure LDAP often fails audits | Secure LDAP supports compliance
- Attack Surface: Insecure LDAP enables lateral movement | Secure LDAP restricts it
Consequences of Using Insecure LDAP
Organizations that continue to rely on insecure LDAP face serious operational and security consequences:
- Active Directory credential compromise
- Privilege escalation and domain takeover
- Regulatory fines and failed compliance audits
- Increased ransomware and insider threat risk
Why Secure LDAP Is Critical for Modern Organizations
Secure LDAP is no longer optional. It is a foundational control for protecting identity infrastructure, especially in hybrid, cloud, and remote work environments.
- Protects credentials across internal and external networks
- Reduces attack vectors used by advanced threat actors
- Supports Zero Trust and modern identity security models
Real-World Security Guidance
Industry leaders and security frameworks strongly recommend disabling insecure LDAP:
- Microsoft LDAP Security Guidance
- MITRE ATT&CK – Man-in-the-Middle
- CISA Identity Protection Recommendations
Best Practices for Securing LDAP
- Disable plaintext LDAP where possible
- Enforce LDAP signing and channel binding
- Deploy valid TLS certificates on directory servers
- Monitor LDAP traffic for anomalies
Final Thoughts
Insecure LDAP remains one of the most exploited weaknesses in enterprise environments. Transitioning to Secure LDAP significantly reduces credential theft, lateral movement, and compliance risk.
Need help securing your identity infrastructure?
Explore iSECTECH Cybersecurity Services or
contact our security experts today.