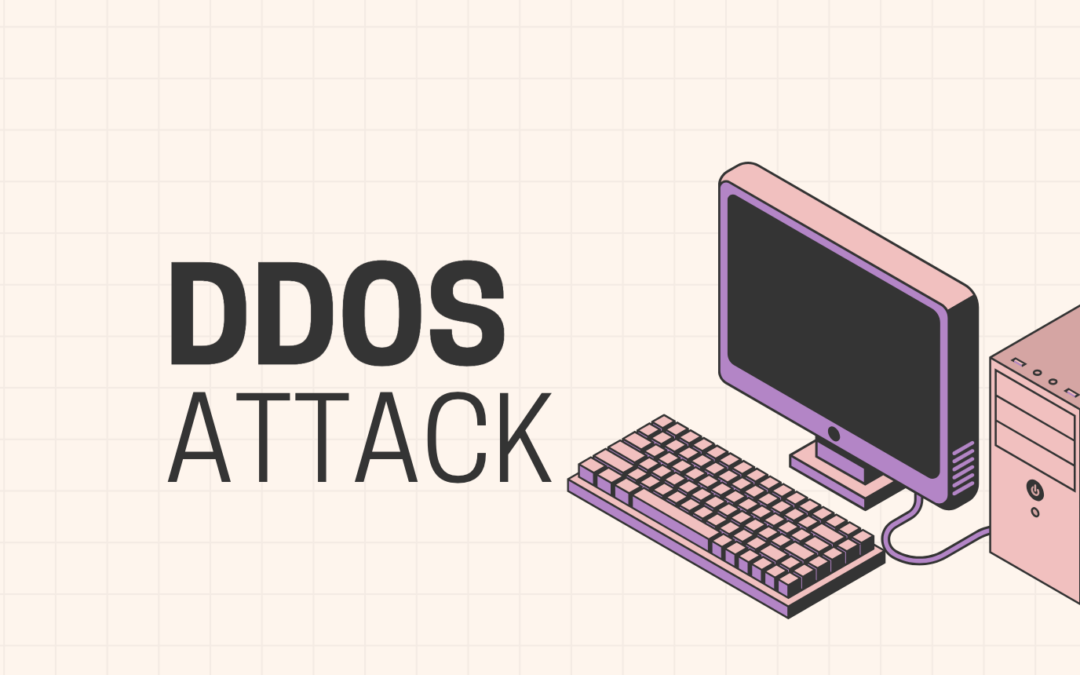
by valino | Mar 12, 2025 | Hacking
With DDoS attacks continuously evolving and becoming more sophisticated, organizations face escalating risks to their digital infrastructure. Drawing on 30 years of cybersecurity and IT consulting experience, this guide explains how DDoS attacks operate, their...

by valino | Mar 7, 2025 | Phishing
Introduction to AI-Generated Threats Artificial Intelligence (AI) has revolutionized numerous industries, from automation to personalized recommendations. However, AI also poses significant threats in the form of deepfakes, realistic but fabricated media designed to...
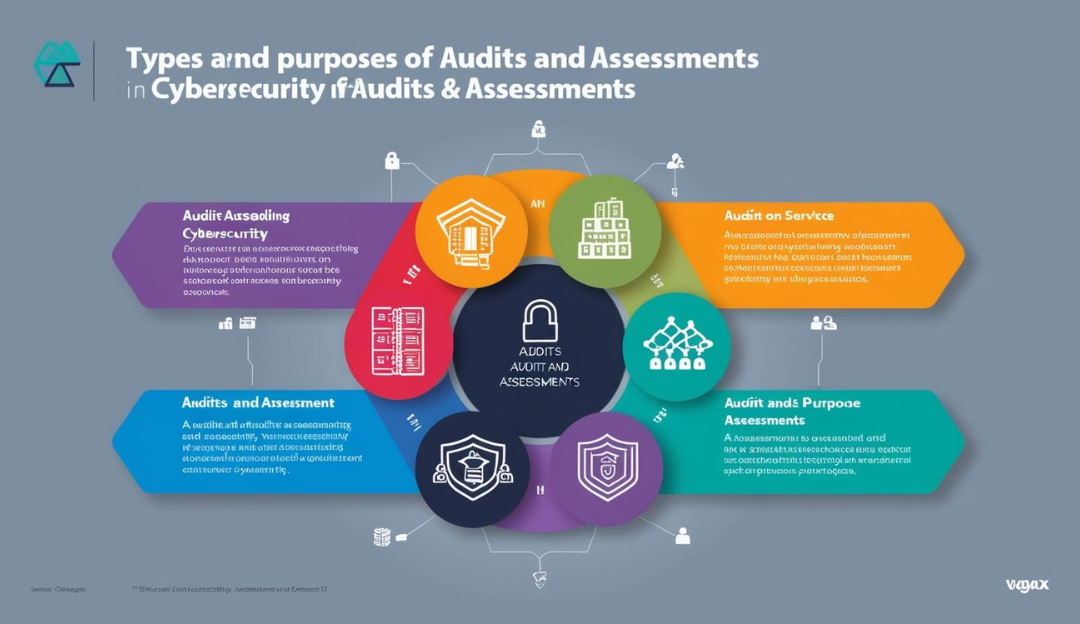
by valino | Jan 23, 2025 | Compliance
In the fast-paced digital landscape, ensuring robust cybersecurity is more critical than ever. Regular audits and assessments are vital tools for identifying vulnerabilities, ensuring compliance, and building a strong defense against cyber threats. In this article,...

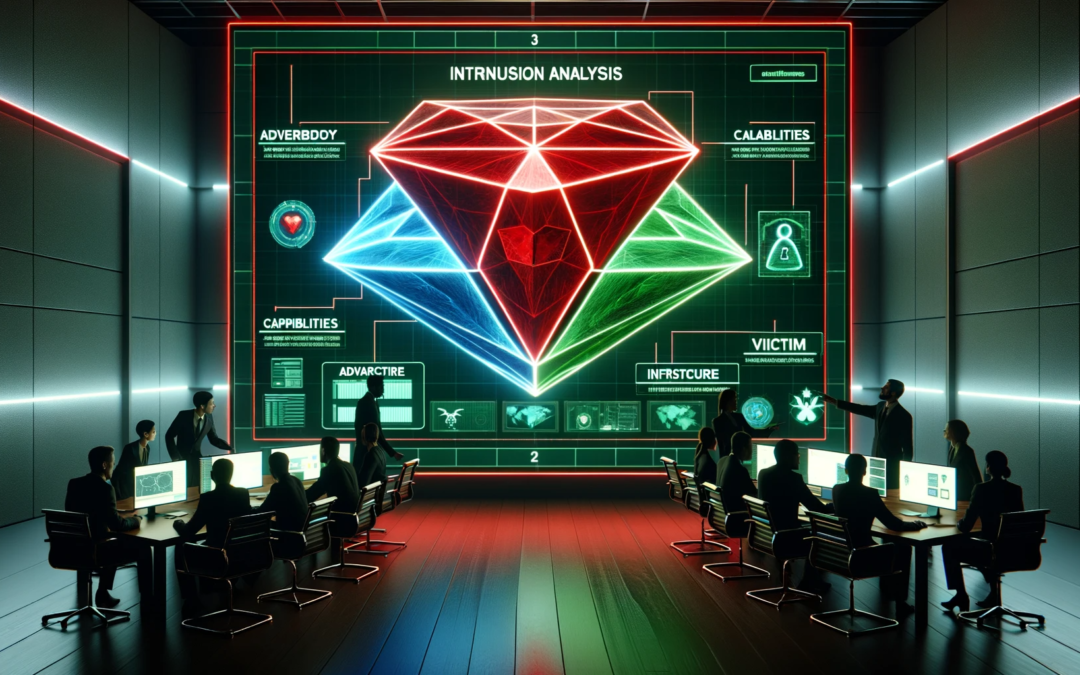
by valino | Jan 23, 2025 | SOC
In today’s digital age, cyber threats are an ever-present concern for organizations, regardless of their size or industry. Implementing security awareness practices isn’t just an option—it’s a necessity. This article will provide an in-depth look at how organizations...

by valino | Nov 9, 2024 | Hacking
As children become digitally connected at younger ages, teaching cybersecurity concepts early is no longer optional—it is essential. With decades of cybersecurity experience, this guide explains how parents, schools, and organizations can help children develop digital...
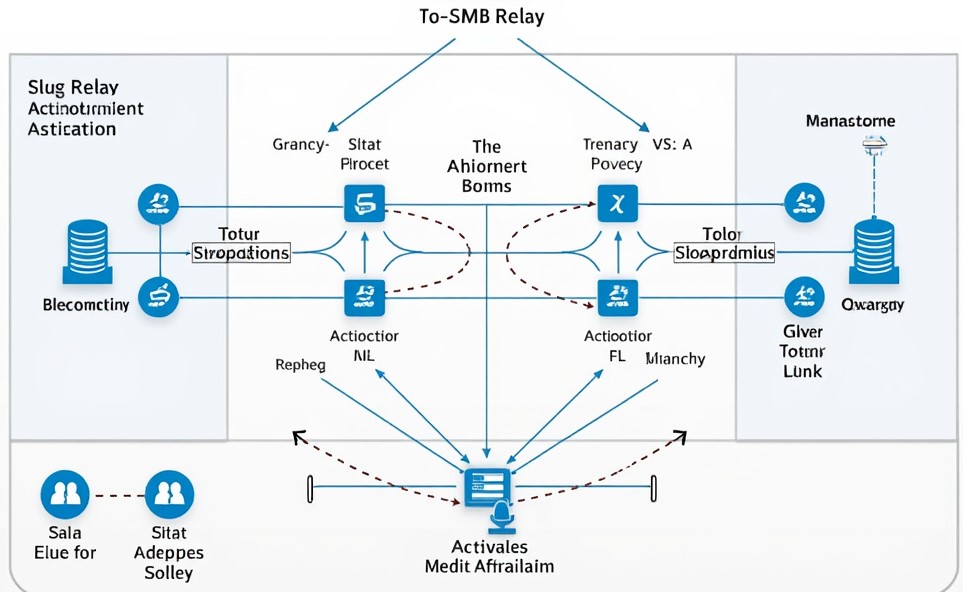
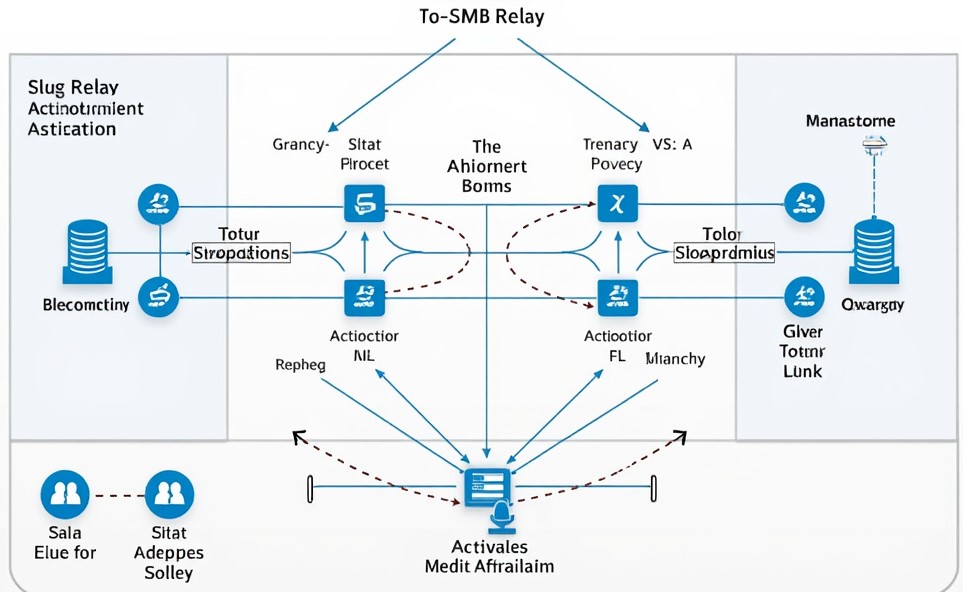
by valino | Aug 29, 2024 | Active Directory
0. Overview Many organizational networks rely on Active Directory (AD) to streamline administrative tasks and enhance efficiency. However, in its default configuration, AD introduces “features” that attackers could exploit. The SMB (Server Message Block) protocols...

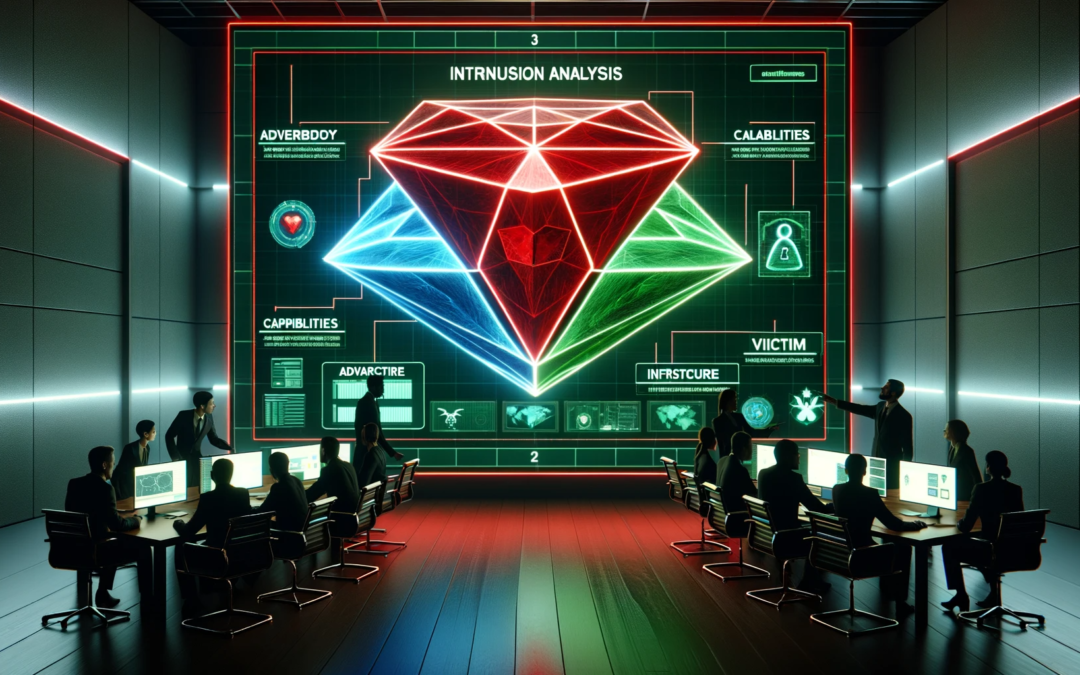
by valino | Jun 10, 2024 | pentesting
Introduction Penetration testing, or “pentesting,” is an essential component of a robust cybersecurity strategy. It involves simulating cyberattacks to identify vulnerabilities in a system before malicious actors can exploit them. While system...
by valino | May 14, 2024 | pentesting
Technology evolves for both the good and bad. Tech gurus create new software and systems to make processes more accessible, efficient, and precise; while on the other hand, hackers evolve their techniques to exploit IT infrastructure weaknesses. That’s why companies...
by valino | Feb 27, 2024 | Web App Pentesting
Race conditions in the realm of cyber security are critical vulnerabilities that can lead to unpredictable outcomes, potentially compromising the security of software systems. This post is designed to demystify this complex concept, breaking it down into easily...

by valino | Feb 13, 2024 | Compliance
Introduction to GDPR The General Data Protection Regulation (GDPR) stands as a monumental piece of legislation within the European Union, aimed at strengthening and unifying data protection for all individuals. Its introduction marked a significant shift in the data...