by valino | May 22, 2026 | Network, Hacking
The most consequential OT security incident we worked in 2026 was caused by a domain administrator’s laptop, not by an attacker who understood industrial control systems. The attacker pivoted from a phished IT user to a flat network where the operational...

by valino | May 21, 2026 | Hacking, Compliance
The most underappreciated reality of ransomware economics in 2026 is that the criminal supply chain has matured into something resembling an enterprise software market. Affiliates pay subscription fees. Builders publish quarterly roadmaps. Negotiators have key...

by valino | May 20, 2026 | Hacking, Compliance
The most useful tabletop exercise we have ever facilitated lasted 90 minutes, involved no slide deck, and produced 14 documented gaps that the company spent the following six months closing. The exercise was deliberately uncomfortable. The CEO did not know the...

by valino | May 19, 2026 | Hacking, Phishing
The most well-meaning phishing simulation program we have audited in 2026 was producing single-digit click rates, glowing quarterly reports to the board, and — in the same period — a 47 percent click rate when an actual phishing crew targeted the organization. The...
by valino | May 19, 2026 | Uncategorized, Compliance
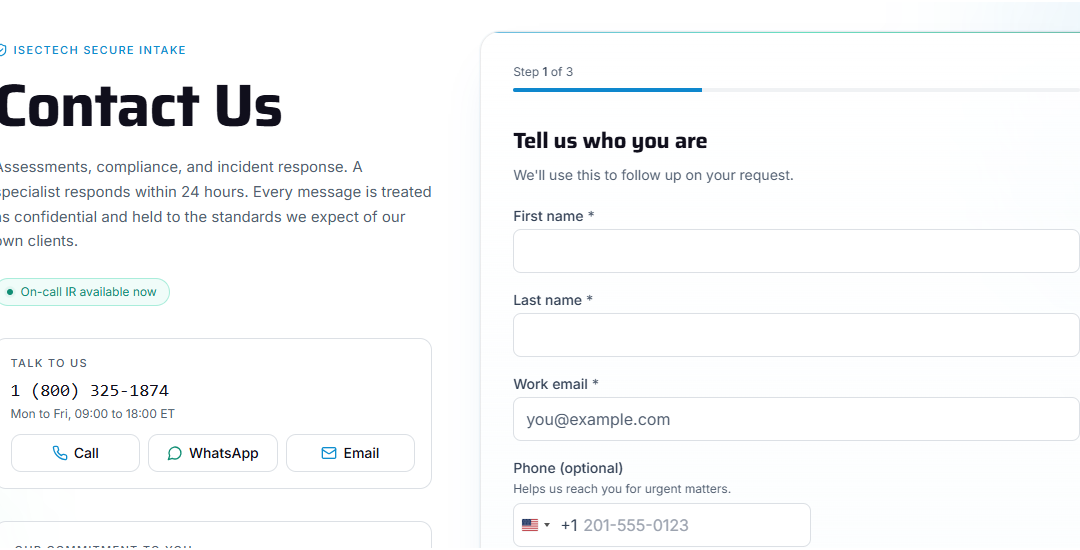
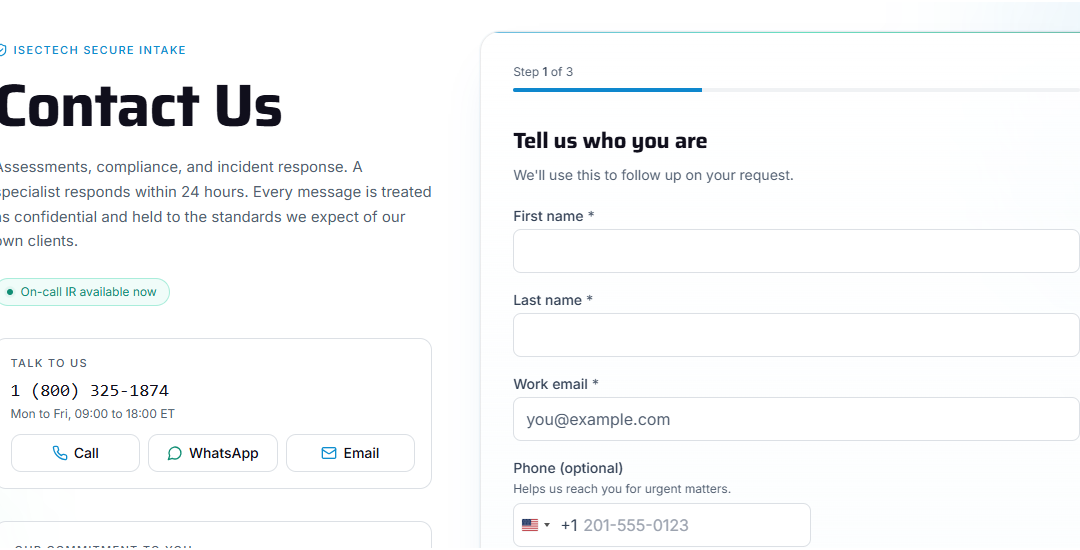
Today we are introducing something we should have had from day one: a contact form built the way a cybersecurity company should build one. We are launching a new contact system, and we are proud of how it treats you and your message. Most contact forms on the web are...

by valino | May 18, 2026 | Hacking, Active Directory
The most expensive privileged access failure we triaged in 2026 came down to a single domain administrator account whose password had not been changed since 2019. The account belonged to a former employee. The password was on a credential dump that surfaced six weeks...

by valino | May 18, 2026 | Hacking, Compliance
This is the second Sunday letter we have written for the CEO who is reading on a quiet evening with the laptop half-closed. The first focused on the questions to ask. This one focuses on the question executives most often avoid: what does cyber liability actually...

by valino | May 16, 2026 | Hacking, Phishing
The MFA fatigue attack we worked last quarter succeeded in eleven minutes. The attacker had a valid username and password — purchased on a credential market for $14 — and used a script to send an authentication push notification to the user’s phone every twenty...

by valino | May 15, 2026 | Hacking, SOC
The most consequential alert fatigue incident we worked in 2026 was not caused by a missed alert. It was caused by a perfectly delivered alert that the on-call analyst dismissed because it was the 3,471st event of his shift. The alert was the first phase of a...

by valino | May 14, 2026 | Hacking, Compliance
The most expensive supply chain attack we triaged in 2026 reached our client through a build dependency that no human had reviewed in three years. A small open-source library — forty-two lines of utility code, sitting four levels deep in the npm dependency graph — had...