by valino | Dec 2, 2023 | Zero-Day
Apple has released software updates for iOS, iPadOS, macOS, and Safari web browser to address two security flaws that it said have come under active exploitation in the wild on older versions of its software. The vulnerabilities, both of which reside in the WebKit web...
by valino | Nov 18, 2023 | SOC
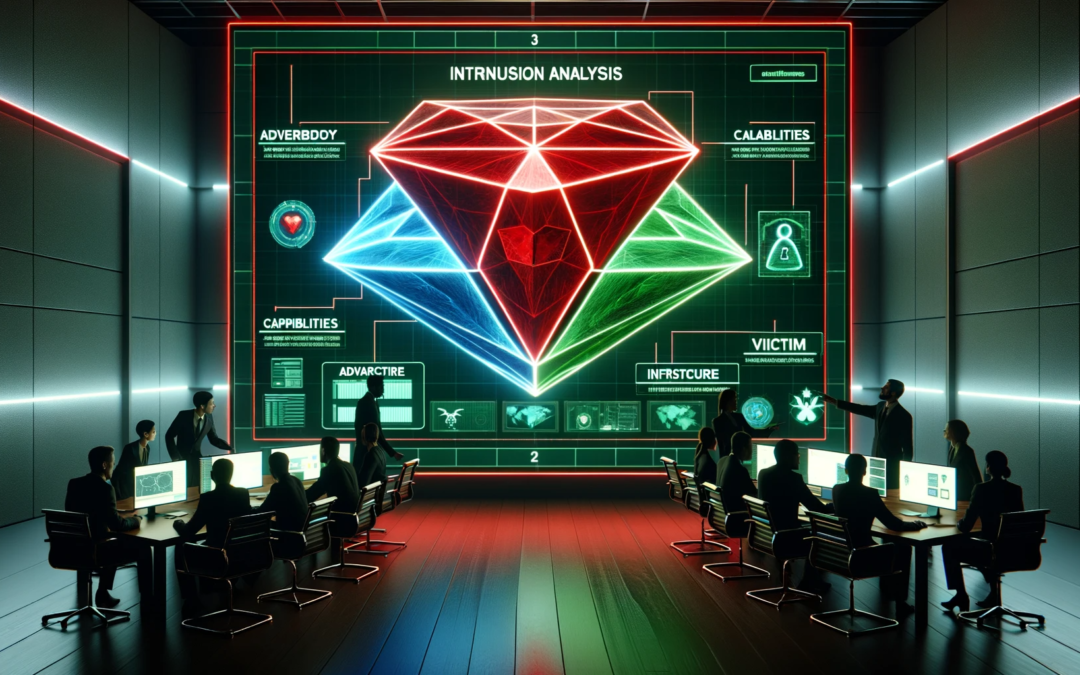
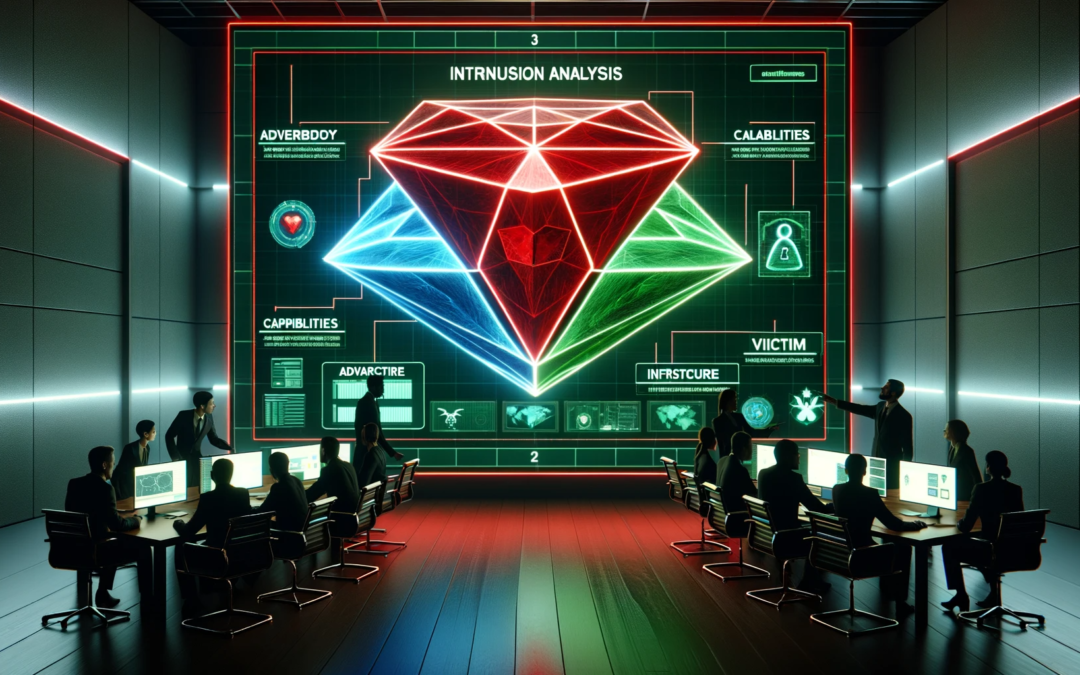
In the complex world of cybersecurity, understanding how attackers operate is crucial for robust defense strategies. Attack frameworks, systematic representations of the tactics, techniques, and procedures (TTPs) used by cyber adversaries, are indispensable tools in...

by valino | Nov 11, 2023 | Network
In the vast universe of cybersecurity, there exists a sentinel known as a reverse proxy, which stands guard between your web server and the relentless sea of internet traffic. Acting as an intermediary, the reverse proxy evaluates requests coming from the internet...

by valino | Nov 11, 2023 | Cryptography
In an era where data breaches are not just incidents but catastrophic events that can define an organization’s future, ISO 27701 emerges as a beacon of guidance for privacy management. As a cybersecurity expert, I will unravel the complexities of ISO 27701,...
by valino | Oct 31, 2023 | Cryptography
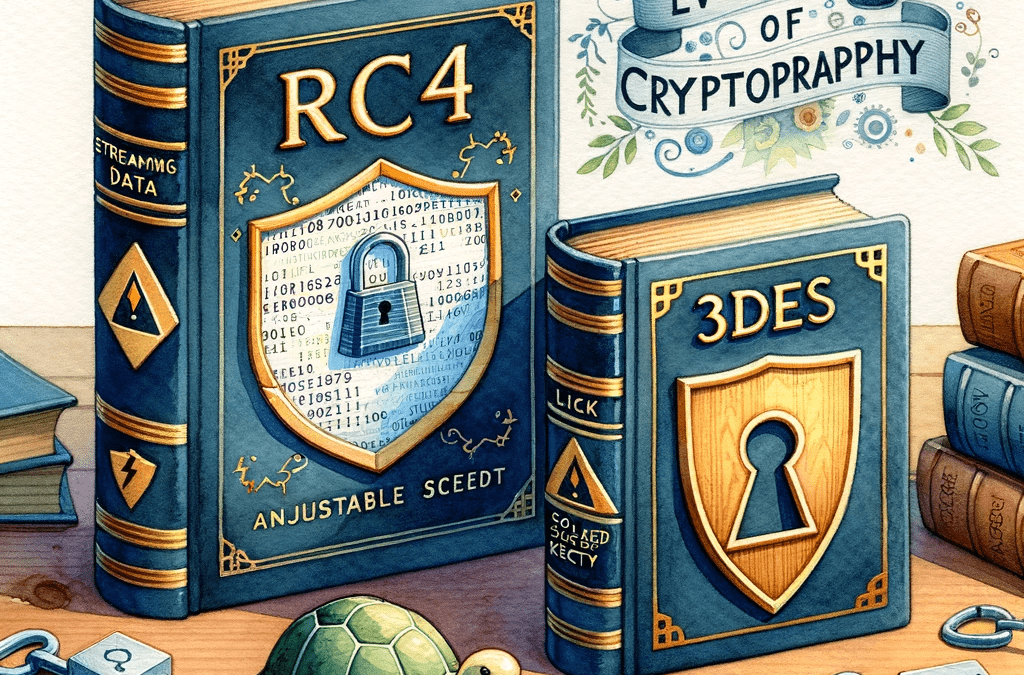
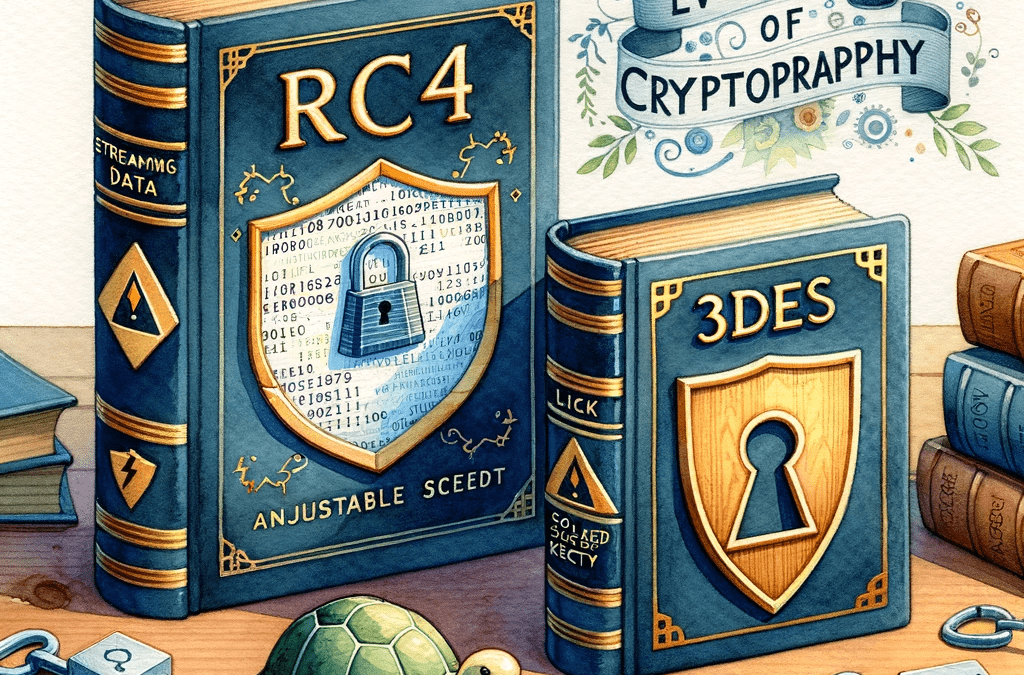
In the world of cryptography, ciphers act as the cornerstone for ensuring the confidentiality and security of data during transmission. Among the myriad of ciphers available, RC4 and Triple DES (3DES) stand as notable mentions. Although both aim to provide data...

by valino | Oct 19, 2023 | SOC
In the digital age, securing your computer against malicious software is akin to locking your doors at night. Viral hacks, encompassing a range of malicious software including viruses, trojans, and worms, pose a constant threat to your data and privacy. Implementing a...

by valino | Oct 19, 2023 | SOC
In the digital age, understanding the intricacies of cyber attacks is crucial. This military concept breaks down the systematic process attackers employ, outlining seven distinct phases. Each phase is a calculated step in the assailant’s strategy, aiming for a...

by valino | Oct 19, 2023 | Web App Pentesting
The Importance of Web App Penetration Testing Methodologies Web application penetration testing, commonly referred to as “pentesting,” is a crucial aspect of any robust cybersecurity strategy. As digital threats continue to evolve, understanding and...

by valino | Oct 16, 2023 | Network
In the realm of network security, ensuring that only authorized individuals have access to your network resources is crucial. One robust method to control this access is through the use of 802.1X authentication. This standard provides a framework for network access...

by valino | Oct 7, 2023 | SOC
In the rapidly evolving domain of cybersecurity, protecting organizational assets from external threats remains a paramount concern. However, an often underestimated source of threat lurks within the very walls of the organization – the internal threat....